Dear readers and customers,
2025 marks our 15th anniversary.
Hooray!
Established in 2010 during our University times, we successfully gave roof to several independent weblogs back then: cipha.net, an Internet anthology. zockerseele.com, all around videogames. As well as gizmeo.eu, for the electronic gadget nerds.
Our vision was simple back then: combine (online) publishing with IT. Twist it, push it. Throw it somewhere and see where it lands.
15 years later we achieved this goal.
Somehow.
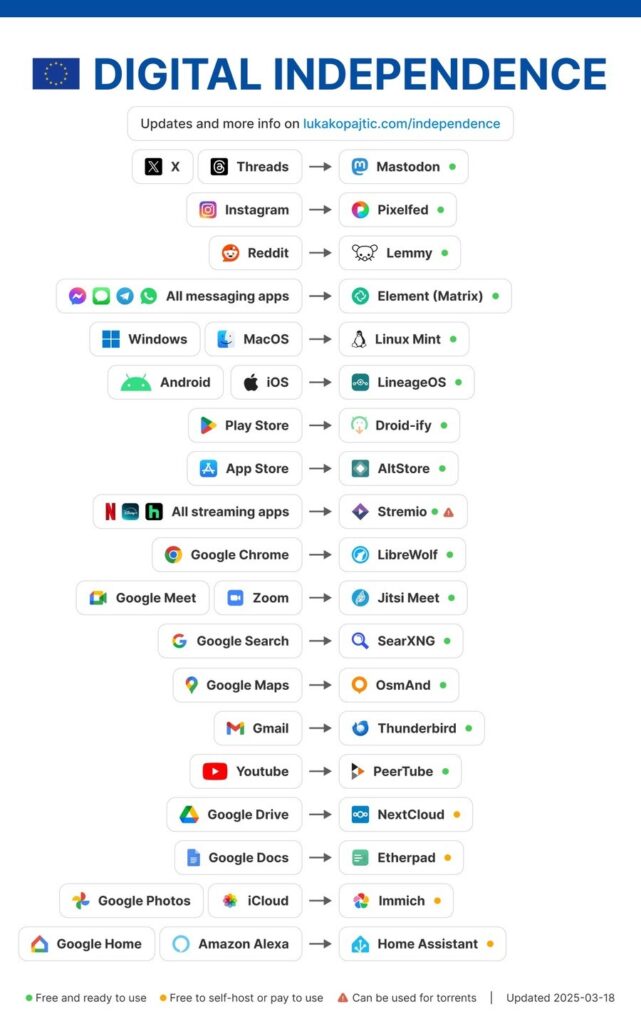
We still build weblogs and give individuals the power of self-publishing. We do the latter too regarding eBooks. We are still doing programming and building Android apps (although those will be delisted publicly as the last store will cease to exist soon. We’ll push the code base to our repo though in the near future). We do cloud hosting with the power of open-source. Plus, we create original merchandise with either artwork created or 100% owned by us. The latter involving trends like blockchain and AI/machine learning also. And all from EU, our beloved and data-safe home.
However, times changed as well as all the technology around it. As such, we won’t be sure if we’ll be around the next 15 years too. And we are not even sad or upset. It’s just, we don’t care anymore. As almost zero of these changes came back in our favour the last 15 years.
Don’t get us wrong: FOSS will stay, we are still a great supporter and nothing we use today or tomorrow will be possible without it. However, we (people or companies who do FOSS) have this curse as nothing we do will generate revenue. Be it short term, long term. Whatever term. We just can’t get rid of this curse. And our perception is (or probably always was), this won’t ever change.
As such, we are not eager to work as hard, work as often and do as much as we did the last decade. There are more rational jobs out there and we all have to eat and pay our bills. We never could do that without the help of the real world. Real world connections, real world work and real world money. Being visionary is one thing. Being able to survive is another.
Or, to stay with the metaphor of 8-ball here: to play the game we need 15 balls (let’s forget the white one for the moment). The game ends when the last one on the table, the black one, is put into the last hole. Let’s just say we reached the point where we are aiming at our last hole here. And believe us we are concentrated, we know exactly what we are doing.
Another truth is, and that’s a nice one: that’s how indie always was. We are able to produce when there’s the right time. We can’t and won’t, when the time is not right. Or the resources are missing. What is the case now doesn’t necessarily need to be the case tomorrow. Better times could be ahead or even worse ones. You never know.
As such, now is the time for us to celebrate! We are still here, we are still recognising technologically interesting times! Just don’t take anything for granted. That’s how life always was, always is, always will be. And if we look inside for a moment and think about it, it’s just perfect that it is like that.
If you can come to Stuttgart or Lisbon, party with us! Drop us a line, give us a call, the next beer is on us. 🙂
Stay sharp and ahead of the game, always,
your aethyx staff